What is ZCash?
Zcash is a decentralized peer-to-peer (P2P) cryptocurrency, that was created as a fork of Bitcoin. Zcash is similar to Bitcoin only in that it also has a 21 million coin supply cap. Otherwise, Zcash separates itself from Bitcoin in that it offers complete (and greater) privacy through cryptographic protocols.
For those coins like Brave’s BAT token, which is privacy and ethic-centric, other developers have looked towards similar mechanisms that offer privacy.
Its founder, Zooko Wilcox serves as both the CEO of both Zcash and the Zerocoin Electric Coin Company, which created the 2013-2014 protocol, Zerocoin (“Zec”). A computer security specialist, Wilcox is the designer of multiple network protocols that incorporate similar concepts like self-contained economies and secure reputation systems.
The Birth of Zcash
Before it came to be known as Zcash, it began as the Zerocoin protocol, serving as a fork of bitcoin’s blockchain. On October 28, 2016, it underwent its first hard fork.
How It Works
Perhaps one of the biggest problems Bitcoin and crypto aimed to solve (and arguably do) for payment networks, is “double spending”. What you need to know is that this isn’t an “accidental” behavior, but everything to do with fraud and misrepresentation.
Double spending is a fraudulent technique where an entity spends the same amount twice. By removing “centralization” or intermediaries, this opened payment networks up to the potential for manipulating balances and transactions.

Do You Want ‘Transparent’ or ‘Private’ Transaction?

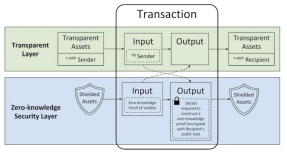
Source: Z Cash
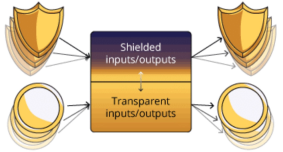
There are two-types of Zcash transactions a normal transparent transaction and a shielded private transaction. Let’s explore both with the following example:
Alice wants to send 1 Zec to Bob. If Bob is okay with keeping the transaction transparent and open for the world to see, then Alice can send him the Zec to his transparent address (“t-addr”).
However, if Bob prefers privacy and doesn’t want the details of his transaction to be open to the public, he can instead have the money send to his shielded address (“z-addr”).
If both Alice and Bob agreed that they want their transaction to be completely private, they can use their shielded addresses to send/receive. By doing this, all the details of the transaction would be private.
If a third-party outside the transaction were to ever get hold of the “private key”, they would have unlimited power to create counterfeit coins something the developers work very hard to prevent. Wilcox has described the private key as “toxic waste” building the protocol’s infrastructure in a way that is designed to keep toxic waste out.
To ensure toxic waste is kept out, a “ceremony” was created. For more information on this, please click here. The best way to visualize the ceremony is similar to how Coca-Cola has protected its most valuable trade secret its recipe. No single person knows the entire recipe, rather, it’s split up amongst a number of selectr individuals, for protection.
By creating a secure multiparty computation, where multiple people each have a piece or “shard” of the public/private key pair, minimizes the chance of someone ever having the whole piece to the puzzle.
Once the computation is created, each member destroys their shard of the private key, and then come together to join the public key shards to create the public key. In essence, if only one participant destroys their private key shard, it will be impossible to recreate.
Even Edward Snowden has lent his support for Zcash in a tweet back in September 2017:

What Makes Zcash “Private?”
The Zerocoin project was created to address bitcoin’s security limitations, that would allow for users to convert their bitcoin to zerocoins, providing additional anonymity by concealing a payment’s origin.
Specifically, the protocol would allow users to split up or alternatively merge zerocoins and even convert them back to bitcoins.
So, how does it work? Zero-Knowledge Proofs. This allows for data to be shared between two parties without the use of a password, but doesn’t prove something with complete certainty. For more information, WIRED Magazine provides a great breakdown.
Z-Cash is able to achieve a high level of privacy because it utilizes Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge, or zk-SNARKS. These come in handy with smart contracts. What Zk-Snarks do is prove that those steps needed to occur in the smart contract, do in fact occur, without revealing what those steps actually are. It essentially protects the individual(s) and the company.
How Does Zk-Snark Work?
A Zk-Snark is made up of three (3) algorithms G, P, and V.
“G” is a key-generator takes an input “lambda”, which is kept confidential at all times, in addition to a program C.
From there, it then proceeds to generate two publicly available keys a proving key pk, and a verification key vk. These keys are made available to any of the parties as well as the public.
“P” is the prover who is going to use 3 items as input proving key pk, the random input x, which is publicly available, and the private statement (“w”) that they want to prove the knowledge of without revealing what it actually is.
The result of the P algorithm generates a proof (“prf”) prf= P(pk, x, w).
“V” is the verifier algorithm returns a boolean variable, which can only be TRUE or FALSE. It takes the verifying key, public input x, and prf
V(vk,x,prf)
The prf returns the entry “TRUE” if the prover is correct, and FALSE if the prover is incorrect.
The Lambda
The value of “Lambda” must always be confidential because it can be used by anyone to generate fake proofs, which would return an entry of TRUE, regardless of whether the prover ever actually acknowledged the private statement (“w”) or not.
Mining ZCash

Source: Blockgeeks
Initially, Zcash implemented a “slow-start mechanism”, which differs than the protocols of many cryptocurrencies, because the number of coins released into the system was much smaller. If a problem was discovered early on, the slow-start mechanism would reduce the impact to blocks. This approach impacted the first 20,000 blocks that were mined over the first month.
Soon after, Zcash began using “equihash”, a proof-of-work algorithm created by Alex Biryukov and Dmitry Khovratovich. The rational behind this is to leave ASIC mining behind for two reasons. For those cryptocurrencies that are ASIC-compatible, make it difficult to mine using CPU or GPU hardware. It makes it very difficult to compete against these ASIC units due to their performance, which of course makes it hard to earn a nice profit.
Second, it allows individuals to get started relatively quickly in Zcash cloud ming without fronting alot of money up-front.
Rather, equihash is predicated upon the “birthday problem”:
If you meet any random stranger out on the streets the chances are very low for both of you to have the same birthday. In fact, assuming that all days of the year have the same likelihood of having a birthday, the chances of another person sharing your birthday is 1/365 which is a 0.27%. However, if you put 20-30 people in a room together, the odds of two people sharing the same birthday increases. At which point, the percentage that 2 people share the same birthday is 50-50.
Remember, Bitcoin monopolizes the mining game by investing large sums of money on ASICs to mine as much bitcoin as possible equihash comes into the picture to make mining as ASIC less centralized and more democratic.
How ZCash is Regulated
On its face, Zcash is difficult to regulate because of its additional security measures. But, nothing is impossible, as law enforcement and regulators are still able to monitor (to an extent) what is happening. This is done through a (1) View Key and (2) Memos.
View Key
Every user has their own view Key, which they can share (as needed) with someone else. The view key removes the ******* so to speak from the transaction, making the transactions completely viewable. With a view key, anyone will be able to see that particular individual’s transactions (its history) and the address of the recipient.
Memos
All Zcash transactions come with a Memo field, which provides additional information only viewable to the recipient. This could include data between financial institutions, as required by law (CCPA, GDPR, etc.).
Making History:
The First ‘Friendly’ Fork to Privatize Mining
On July 19, 2020, Zcash made history as the first cryptocurrency to have a “friendly” network split for the purpose of privatizing mining something that hadn’t been done before. In a tweet by the Ycash Foundation, the first Ycash block was mined on July 16.
The “friendly” fork, Heartwood, is the privacy coin’s fourth hard fork since the company launched in late 2016m bringing two specific updates to the ecosystem, referred to as Zcash Improvement Proposals (ZIPs).
The first, “Shielded Coinbase”, or ZIP 213, brings additionally sought-out privacy solutions for ZEC mining, while “Flyclient”, or ZIP 221 adds support for lightweight clients that verify transactions.
In December 2019, the company underwent its third hardfork, “Blossom”. Heartwood is supported by both the Electric Coin Company (ECC), the for-profit development house behind the project, and Zcash Foundation.
The latest fork will “restore a goal” of mining on commodity hardware, according to the Foundation.
Shielded Coinbase
Shielded coinbase transactions allow miners to claim Coinbase transactions, their reward for processing transactions, directly to Zcash’s shielded addresses. These addresses hides or obfuscates transaction amounts, other addresses, and the envrypted memo field.
Implementing these “private” Coinbase transactions began in 2018 with the company’s second hard fork, “Sapling”.
Flyclient
Flyclient allows users to verify transactions with the smallest amount of information possible maintaining as much privacy as possible. Similar to Bitcoin’s SPV nodes, or Simplified Payment Verification nodes, this also proves the knowledge of a transaction only using the block header, rather than the full content of the block.
These two updates have presented Zcash the ability to serve as a gateway into Ethereum’s DeFi ecosystem.